很多网站或应用登录验证除了账号密码外还加了二次验证,有短信验证码、邮箱验证码的,Google Authenticator二次验证使用范围也越来越广泛了。
一、说明
一般都是基于时间戳的Google Authenticator动态口令,这是一个每隔30s会动态生成一个6位数的数字,只要手机端时间与服务器时间误差不超过30秒,基本上生成生成动态口令一致。
二、操作过程
1、 下载 Google 身份验证器
2、 生成秘钥
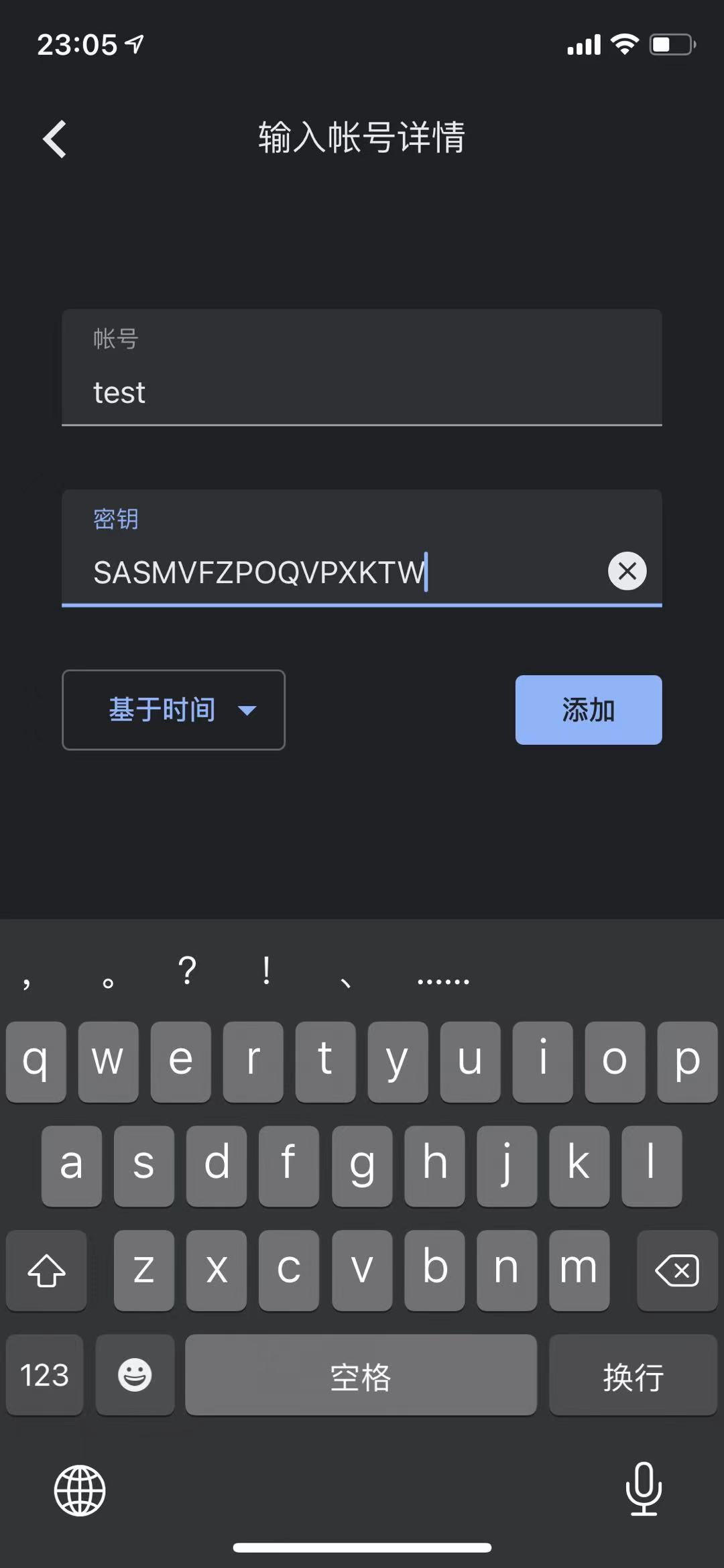
使用代码中的GetSecret()函数生成密钥字符串,然后将字符串保存到用户登录信息中,然后将密钥字符串添加到 Google 身份验证器中
3、验证字Google Code
将Google 身份验证器中的Google Code 6位数字输入验证VerifyCode(secret string, code int32) bool

三、实现代码
// @Title
// @Description $
// @Author 55
// @Date 2021/9/16
package main
import (
"crypto/hmac"
"crypto/rand"
"crypto/sha1"
"encoding/base32"
"fmt"
"strings"
"time"
)
func main() {
fmt.Println("----------------- 生成secret -------------------")
secret := GetSecret()
fmt.Println("secret:" + secret)
fmt.Println("----------------- 信息校验----------------------")
var code int32
fmt.Print("请输入Google Code:")
for {
_, err := fmt.Scan(&code)
if err == nil {
break
}
fmt.Print("输入错误,请重新输入:")
}
b := VerifyCode(secret, code)
if b {
fmt.Println("验证成功!")
} else {
fmt.Println("验证失败!")
}
}
func GetSecret() string {
randomStr := randStr(16)
return strings.ToUpper(randomStr)
}
func randStr(strSize int) string {
dictionary := "ABCDEFGHIJKLMNOPQRSTUVWXYZ"
var bytes = make([]byte, strSize)
_, _ = rand.Read(bytes)
for k, v := range bytes {
bytes[k] = dictionary[v%byte(len(dictionary))]
}
return string(bytes)
}
// 为了考虑时间误差,判断前当前时间及前后30秒时间
func VerifyCode(secret string, code int32) bool {
// 当前google值
if getCode(secret, 0) == code {
return true
}
// 前30秒google值
if getCode(secret, -30) == code {
return true
}
// 后30秒google值
if getCode(secret, 30) == code {
return true
}
return false
}
// 获取Google Code
func getCode(secret string, offset int64) int32 {
key, err := base32.StdEncoding.DecodeString(secret)
if err != nil {
fmt.Println(err)
return 0
}
// generate a one-time password using the time at 30-second intervals
epochSeconds := time.Now().Unix() + offset
return int32(oneTimePassword(key, toBytes(epochSeconds/30)))
}
func toBytes(value int64) []byte {
var result []byte
mask := int64(0xFF)
shifts := [8]uint16{56, 48, 40, 32, 24, 16, 8, 0}
for _, shift := range shifts {
result = append(result, byte((value>>shift)&mask))
}
return result
}
func toUint32(bytes []byte) uint32 {
return (uint32(bytes[0]) << 24) + (uint32(bytes[1]) << 16) +
(uint32(bytes[2]) << 8) + uint32(bytes[3])
}
func oneTimePassword(key []byte, value []byte) uint32 {
// sign the value using HMAC-SHA1
hmacSha1 := hmac.New(sha1.New, key)
hmacSha1.Write(value)
hash := hmacSha1.Sum(nil)
// We're going to use a subset of the generated hash.
// Using the last nibble (half-byte) to choose the index to start from.
// This number is always appropriate as it's maximum decimal 15, the hash will
// have the maximum index 19 (20 bytes of SHA1) and we need 4 bytes.
offset := hash[len(hash)-1] & 0x0F
// get a 32-bit (4-byte) chunk from the hash starting at offset
hashParts := hash[offset : offset+4]
// ignore the most significant bit as per RFC 4226
hashParts[0] = hashParts[0] & 0x7F
number := toUint32(hashParts)
// size to 6 digits
// one million is the first number with 7 digits so the remainder
// of the division will always return < 7 digits
pwd := number % 1000000
return pwd
}
四、测试
----------------- 生成secret -------------------
secret:SASMVFZPOQVPXKTW
----------------- 信息校验----------------------
请输入Google Code:199186
验证成功!



评论区